Filtering and sorting events in app review
RocketCyber provides an intuitive triage view interface that allows users to effortlessly sort and filter event data for faster analysis.
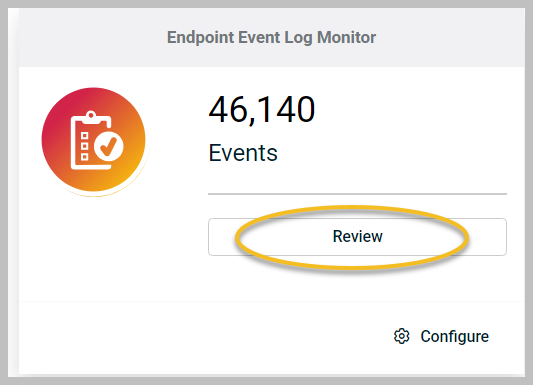
Accessing event triage
-
In the RocketCyber dashboard, click Review on any app card.
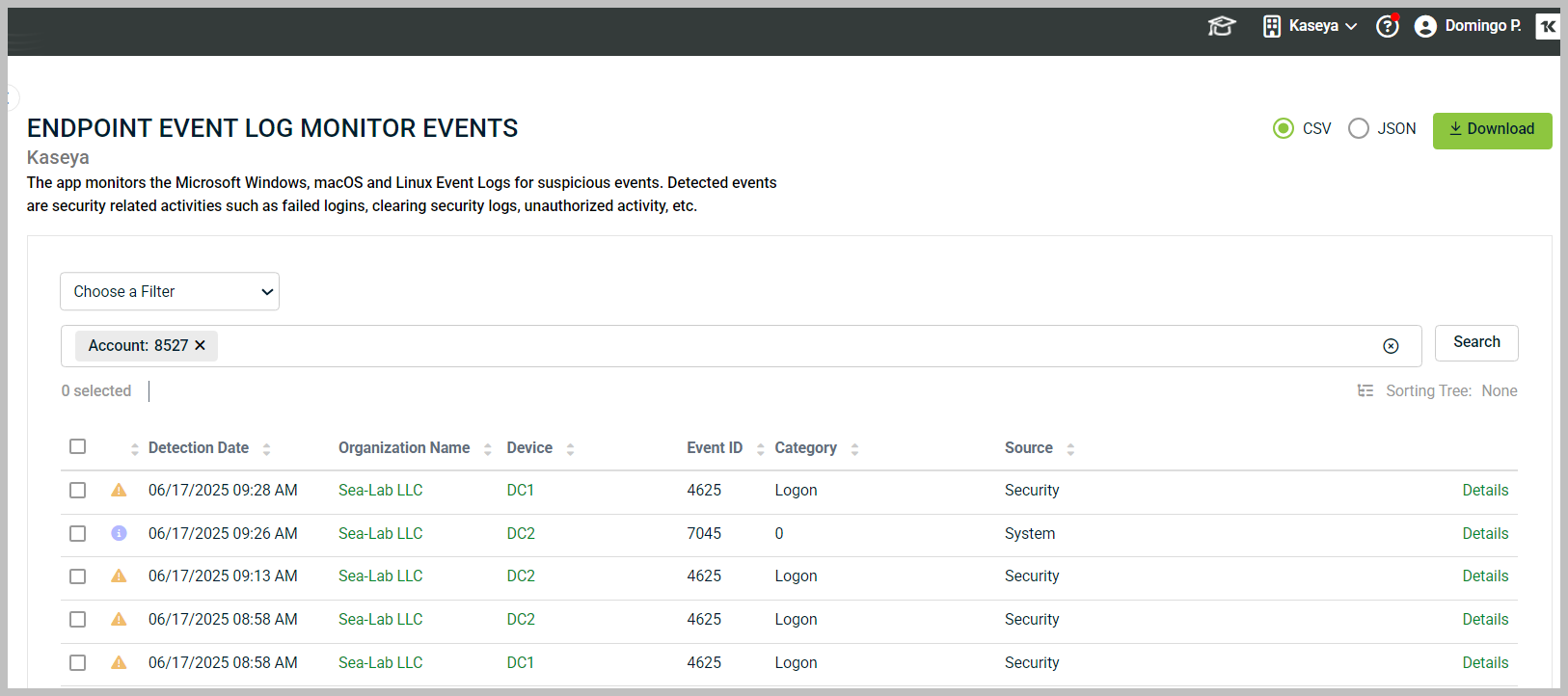
2. The event triage page will appear. At the top of the page, you will see the search/filter interface.
-
The default filter displays events relevant to the current account context.
-
The main area, called the event grid, shows event data in rows and columns.
Sorting columns
You can sort events by clicking any column header in the event grid. Available columns include:
- Detection Date
- Organization Name
- Device
- Event ID
- Category
- Source
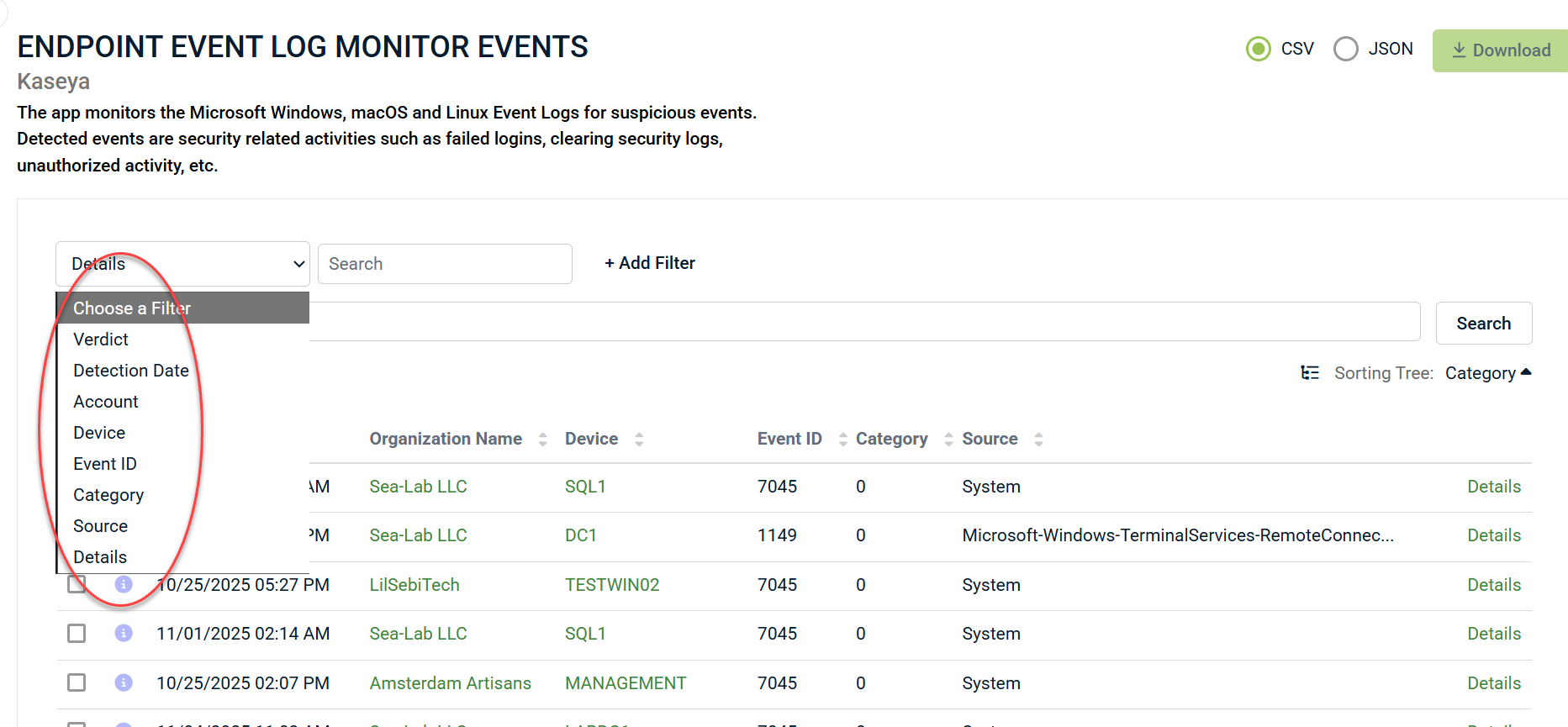
Filtering data
The search/filter interface provides quick ways to filter data based on the app being reviewed. For example, in the Endpoint Event Log Monitor app, default search fields include:
- Verdict
- Detection Date
- Account
- Device
- Event ID
- Category
- Source
- Details
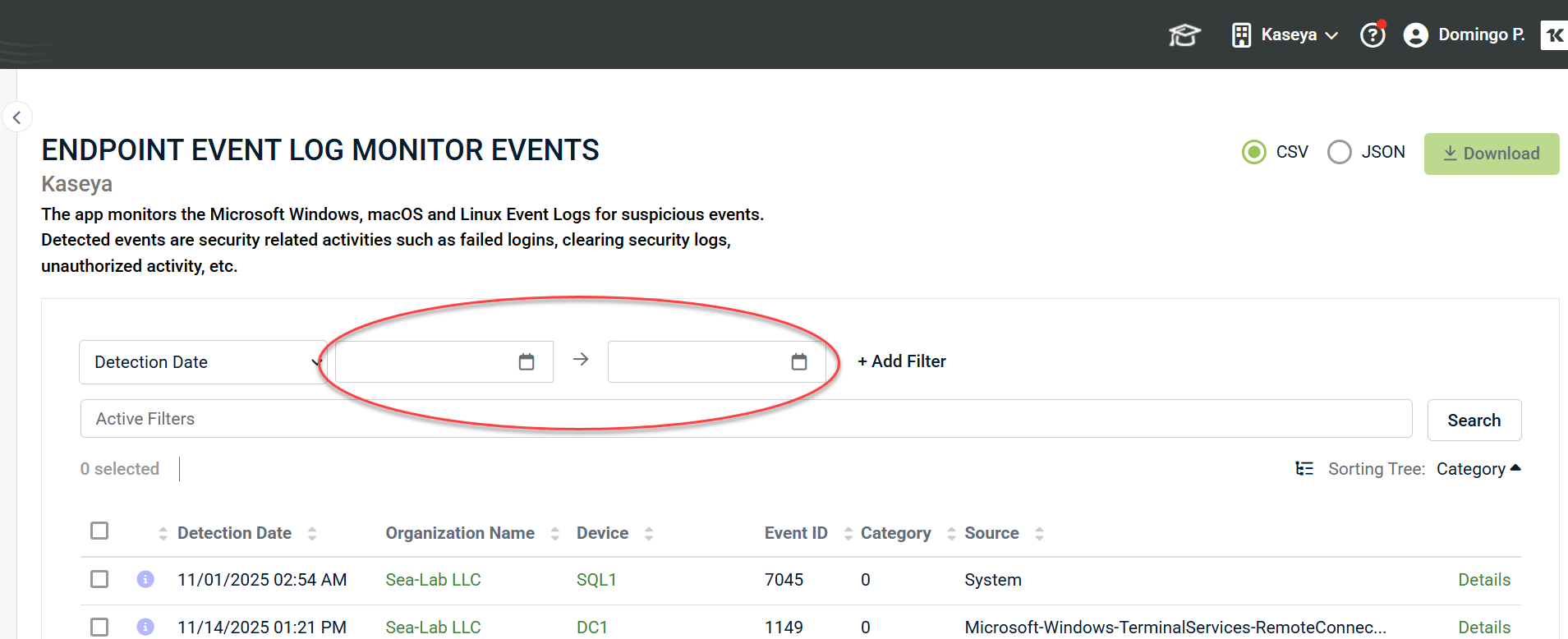
Example: Filter by Detection Date
1. Select Detection Date from the filter list.
2. Enter a date range.
3. Click + Add Filter, then Search.
NOTE Choosing a single Detection Date returns all events from that date through to the current date and time.
Filtering by multiple criteria
You can combine filters using AND logic.
Example: Filter by Detection Date and Event ID:
1. Add Detection Date filter for 11/01/2025–12/18/2025.
2. Add Event ID filter with value 131.
3. Click Search.
NOTE Results will only display events matching both criteria.
Advanced filtering: JSON attributes
Events can be filtered by attributes found in the event details JSON. To review attributes, do as follows:
1. Download the JSON from the console.
2. Analyze its structure.
For Endpoint Event Log details, the structure may look like this:
{
"type": "EventLogMonitor",
"attributes":
{
"xml": "<Event xmlns='http://schemas.microsoft.com/win/2004/08/events/event'><System><Provider Name='Microsoft-Windows-Eventlog' Guid='{fc65ddd8-d6ef-4962-83d5-6e5cfe9ce148}'/><EventID>104</EventID><Version>0</Version><Level>4</Level><Task>104</Task><Opcode>0</Opcode><Keywords>0x8000000000000000</Keywords><TimeCreated SystemTime='2022-04-03T04:49:54.696269100Z'/><EventRecordID>1507515</EventRecordID><Correlation/><Execution ProcessID='980' ThreadID='992'/><Channel>System</Channel><Computer>Joe-User.rocketcyber.com</Computer><Security UserID='S-1-5-18'/></System><UserData><LogFileCleared xmlns='http://manifests.microsoft.com/win/2004/08/windows/eventlog'><SubjectUserName>SYSTEM</SubjectUserName><SubjectDomainName>NT AUTHORITY</SubjectDomainName><Channel>Windows PowerShell</Channel><BackupPath></BackupPath></LogFileCleared></UserData></Event>",
"opcode": "Info",
"message": "The Windows PowerShell log file was cleared.",
"version": 0,
"event_id": 104,
"log_name": "System",
"record_id": 1507515,
"telemetry":
{
"event_sent_to_cloud": 1648961394.733,
"event_sent_to_cloud_t": "2022-04-02 23:49:54",
"event_log_msg_recieved": 1648961394.732,
"event_log_msg_recieved_t": "2022-04-02 23:49:54",
"event_log_msg_passed_post_app_result": 1648961394.733,
"event_log_msg_passed_post_app_result_t": "2022-04-02 23:49:54"
},
"event_time": 1648961394,
"event_type": "Information",
"source_name": "Microsoft-Windows-Eventlog",
"computer_name": "Joe-User.rocketcyber.com",
"event_category": "Log Clear"
}
}
If we want to search details for an attribute such as event_category, choose Details from the search drop-down menu and enter the following text in the search value field:
attributes.event_category:Log Clear
Filtering arrays: targetResources
Some events include a `targetResources` property, which is an array of objects.
IMPORTANT Avoid searching using patterns like `targetResources.value` (for example, `targetResources.userPrincipalName:Rodri7IT@ueoficial.com`). This `.value` pattern assumes you are targeting a single object, not an array. Since `targetResources` is an array, attributes such a `userPrincipalName` exists within each item of the array and cannot be searched directly.
To perform a broad search across the array, use a format like:
targetResources:Rodri7IT@ueoficial.com
Example JSON structure for targetResources array, showing user and group objects
{"targetResources": [
{
"id": "12345",
"type": "User",
"userPrincipalName": "Rodri7IT@ueoficial.com",
"displayName": "Rodrigo IT",
"accountEnabled": true
},
{
"id": "67890",
"type": "Group",
"displayName": "Admins",
"groupType": "Security"
}
]}
CSV Export Notes
When exporting filtered results to CSV:
-
Verdicts are numeric:
-
1 = Informational
-
2 = Suspicious
-
3 = Malicious
-