Understanding the RocketCyber threat map
The RocketCyber Threat Map is a pivotal feature within RocketCyber, designed to visually represent detected cybersecurity threats and their origins. This tool aids in comprehending the cybersecurity landscape by showcasing real-time threat activities, including the geographic sources and targets of malicious traffic that could impact users' environments. It enables the rapid identification of potential attack vectors and helps facilitate preventive security measures. Specifically tailored for Managed Service Providers (MSPs), the Threat Map provides real-time visualizations of malicious and suspicious activities affecting the endpoints they manage.
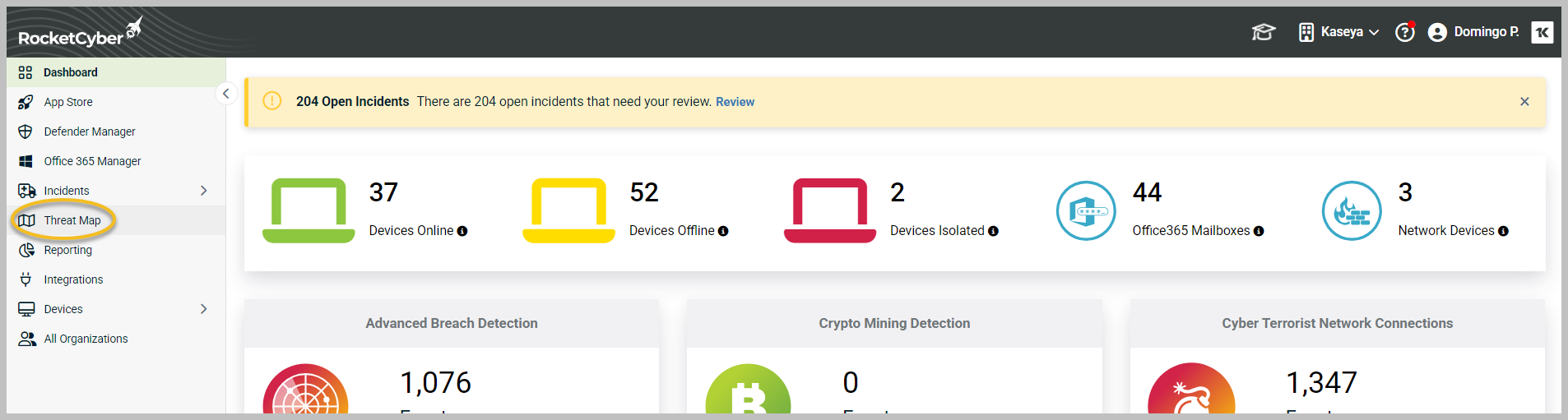
To access the Threat Map, go to the left menu and click Threat Map.
Key features of the RocketCyber Threat Map
-
Visual representation: The Threat Map utilizes a global map interface to display the geographic locations from which cyber threats are originating and targeting. This dynamic visualization allows for a clearer understanding of threat distribution compared to traditional dashboards.
-
Real-time data: Users can benefit from a dynamic view of ongoing threat activities, allowing them to monitor current attacks and emerging risks. The map reflects these threats as they materialize, which is critical for proactive threat management.
-
Actionable insights: The threat map highlights various types of detected threats along with their geographical distribution. This information empowers users to quickly assess the situation and prioritize their responses effectively.
-
Integration with RocketCyber applications: Seamless integration with RocketCyber's suite of threat detection applications—including Breach Detection, Malicious File Detection, and Suspicious Event Monitor—provides a comprehensive security perspective and enhances incident response capabilities. It consolidates data from multiple sources for improved visibility and advanced threat detection.
-
Customer-specific focus: Unlike generic global threat maps, this tool emphasizes activity relevant to the specific clients of the MSP, allowing for tailored threat assessments.
-
Drill-down capabilities: MSPs can view the overall threat landscape across all their customers or delve into threats impacting individual clients.
-
Detailed threat information: The map provides crucial details regarding detected threats:
-
It provides a visual representation of identified threats on the right side. It displays the attacker's location, IP address, and the date and time of detection.
-
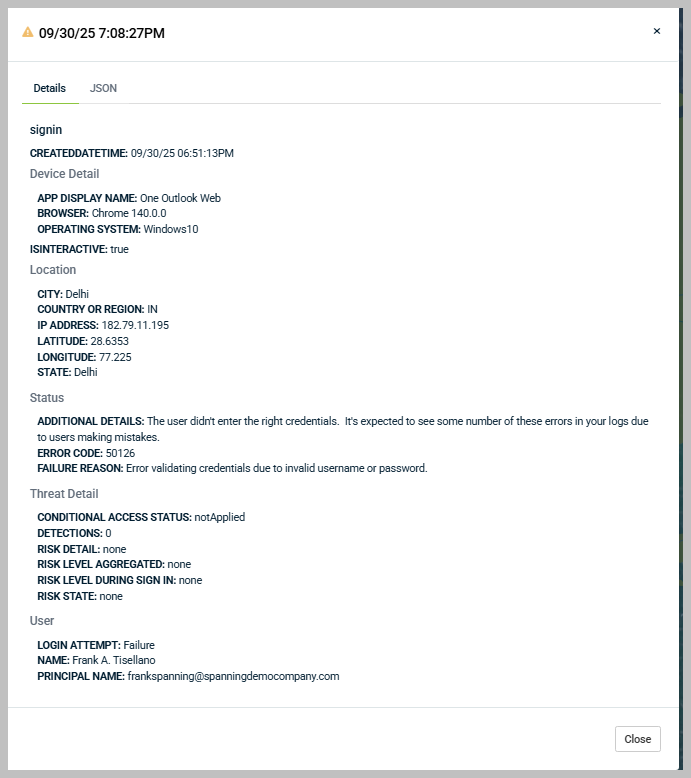
Click Details to view further information about each detected threat.
Users will find details including the origin location and IP address of the attacker, the date and time of detection, device information, additional specifics, error codes, reasons for failure, and the risk level.
-
-
Early warning indicators: The map highlights potential risks, such as unusual SSH or FTP connections from regions known for high cyberattack activity, prompting further investigation. This feature serves as an early warning and visualization tool, offering real-time insights into attacks that may impact users.
The 24/7 RocketCyber Security Operations Center (SOC) team utilizes this information to efficiently investigate and respond to security incidents. They triage alerts based on threat severity, prioritize them, and implement remediation actions, which may include leveraging automated response and isolation technologies. The SOC team collaborates with IT partners to develop coordinated remediation plans.
In essence, the RocketCyber Threat Map equips MSPs with a comprehensive visual understanding of the threats impacting their clients, facilitating quicker and more effective remediation efforts. Integrating with its Managed SOC, detection apps, and broader platform functionalities, it provides a holistic and actionable view of security threats.